SHA256: bdf243b7a296f7aecc366c799e3fb865ee3aff7c72d8d942e2b2632a347fe5c3
I downloaded this sample from Malshare.
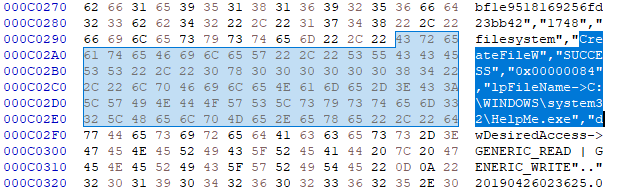
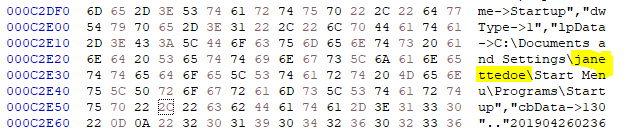
I started decoding PE hex to text file and found that the PE file has embedded another file which will be dropped on execution.
Filename: help.exe
SHA256: 837bef64239be017a2aac92852576efc7d84774d90f64e9d69c5cc3a2b4ecce4
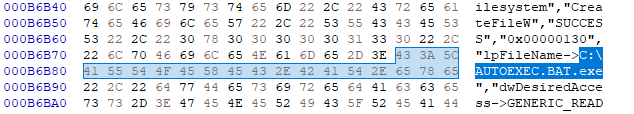
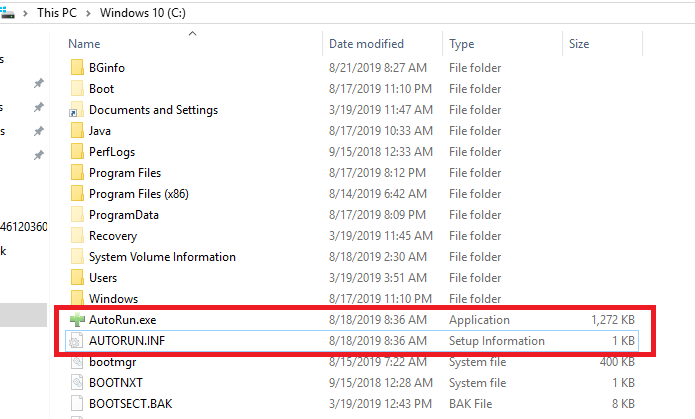
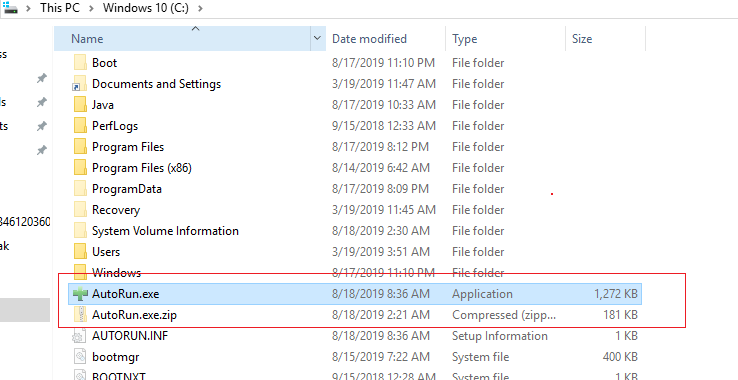
It also drops Autoexec.bat.exe file and Autoexec.exe files at C:\ location. (But it didn’t drop these files instead it dropped AutoRun.INF and AutoRun.exe)
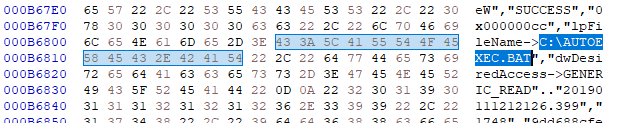
Also found computer username emartinez in path to PDB file, that means this file must be compiled on a machine under this user account.
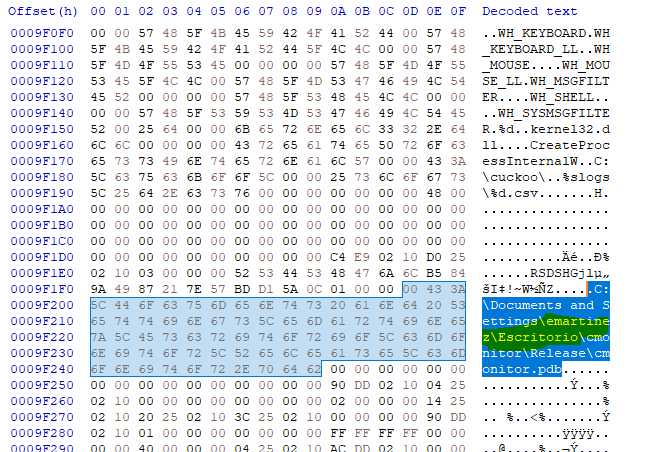
and username janettedoe in another path to startup programs
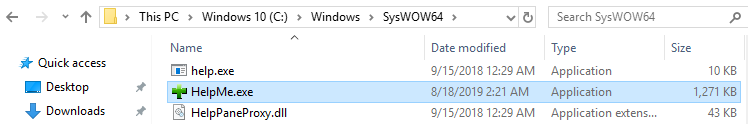
I executed this PE file for dynamic analysis. I found this file dropped Helpme.exe, AutoRun.INF same location I have seen in hex code.
Files Dropped:
- C:\Windows\System32\HelpMe.exe
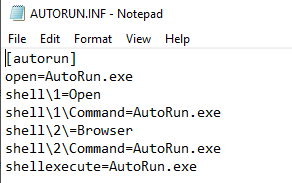
- C:\AutoRun.INF
- C:\AutoRun.exe
Screenshots
AUTORUN.INF file at location C:\
AUTORUN.INF file executes executable AutoRun.exe file. (Below screenshot)
Another executable dropped at below location
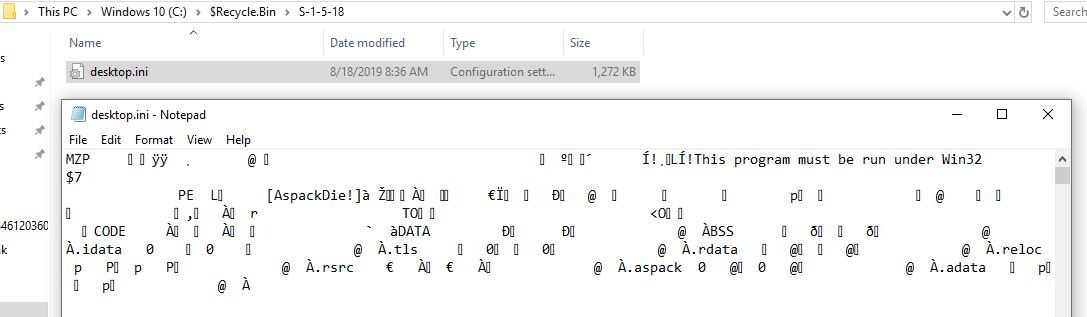
C:\$Recycle.Bin\S-1-5-18
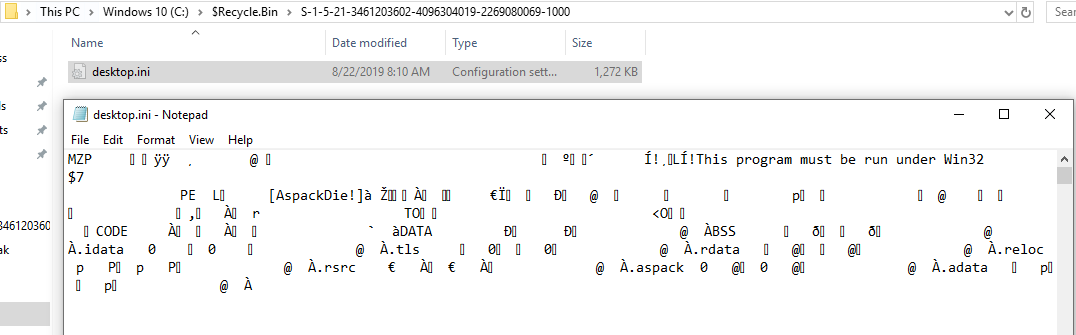
C:\$Recycle.Bin\S-1-5-21-3461203602-4096304019-2269080069-100
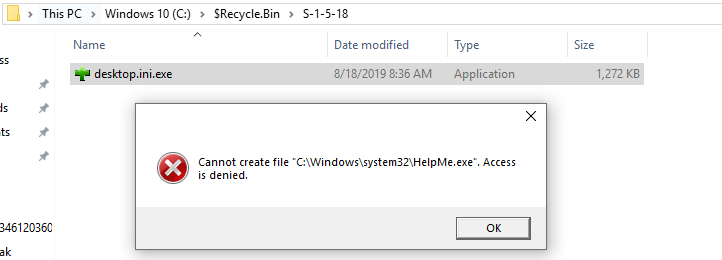
I did rename C:\$Recycle.Bin\S-1-5-18\desktop.ini file to desktop.ini.exe and double click to execute it. It has given error Cannot create file “C:\Windows\System32\HelpMe.exe
Then I executed desktop.ini.exe file with administrative privilege (before execute this file I had commented AutoRun.exe file at location C:\) and this file executed C:\Windows\System32\HelpMe.exe which dropped file AutoRun.exe at location C:\
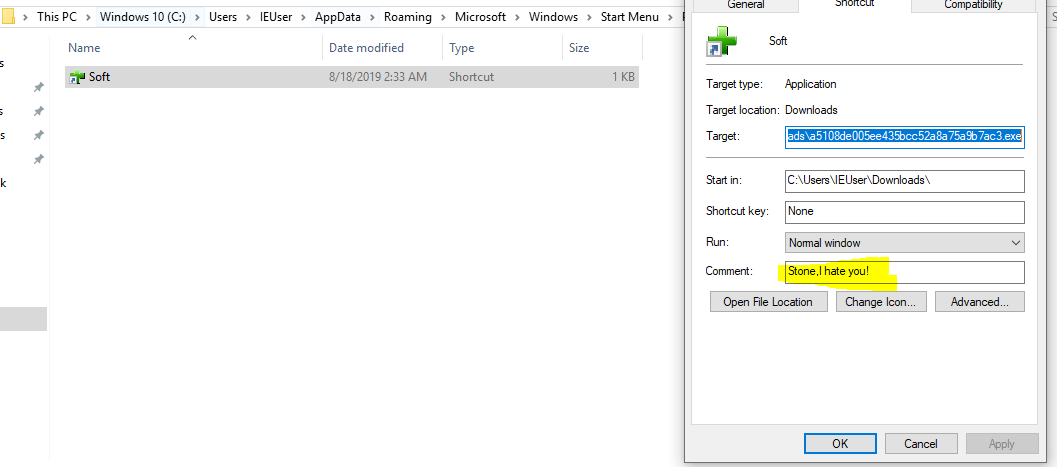
I disassembled AutoRun.exe file and found this creates file Soft.lnk which again has path to execute HelpMe.exe on windows startup.
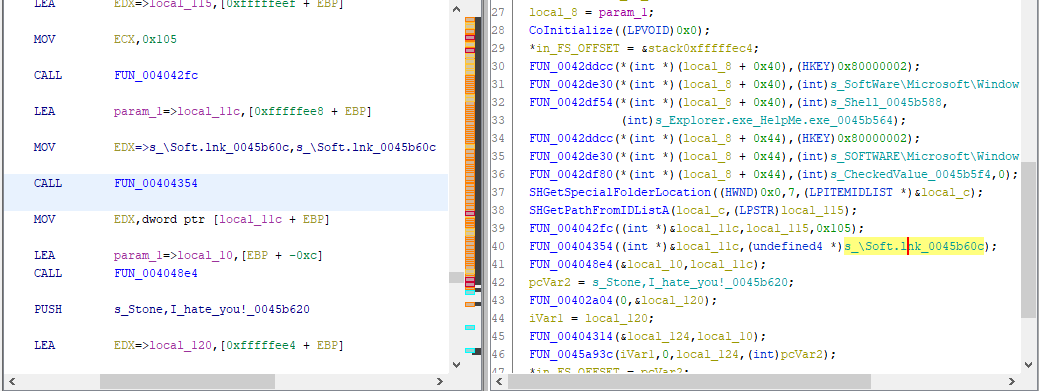
Below soft.lnk has comment Stone, I hate you! this file has target to execute AUTORUN.INF.exe
No internet connectivity has been tested from this malware, as this analysis done offline.
