In recent weeks, a highly organized phishing campaign has surfaced, characterized by its use of legitimate Google infrastructure to bypass standard security filters. I have identified more than 25 distinct phishing emails targeting a single account, all of which ultimately direct users to a specific URL:
hxxps://storage[.]googleapis[.]com/whilewait/comessuccess.html
Understanding the Technical Infrastructure
The URL in question is hosted on Google Cloud Storage (GCS). To the average user or basic email security gateway, the domain googleapis.com appears trustworthy because it is a legitimate Google-owned domain used for hosting cloud assets.
In this specific exploit:
- The Bucket: whilewait is a unique storage container created by the attacker within a Google Cloud project.
- The Payload: comessuccess.html is a script-heavy file designed to act as a “gatekeeper” or “redirector“.
By hosting the initial link on Google’s servers, the attackers ensure the email passes authentication checks like SPF and DKIM. Once a user clicks, the HTML file on Google’s server silently redirects the browser to a third-party malicious site, often used for credit card harvesting or malware distribution.
Diversity of Social Engineering Tactics
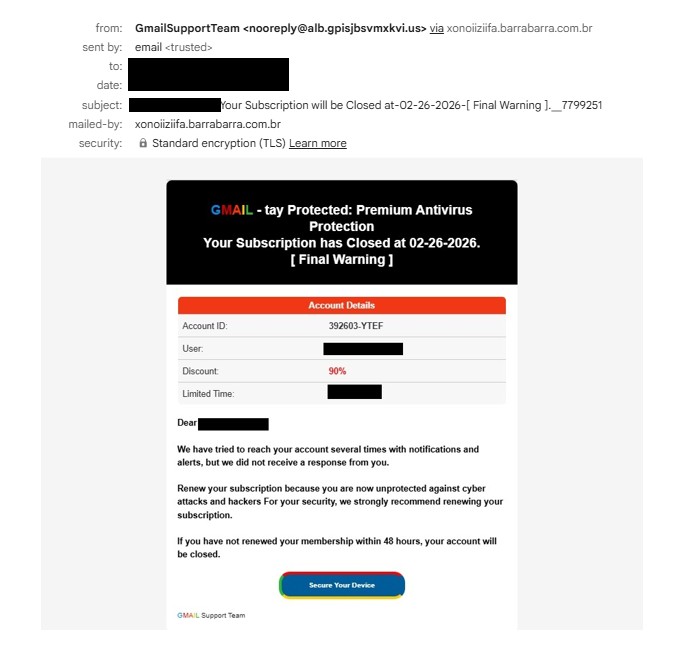
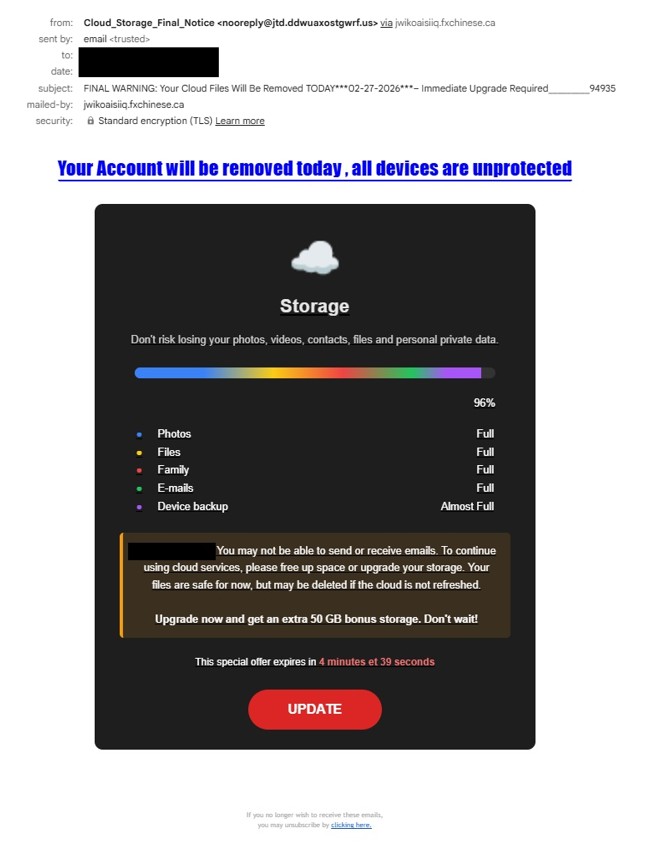
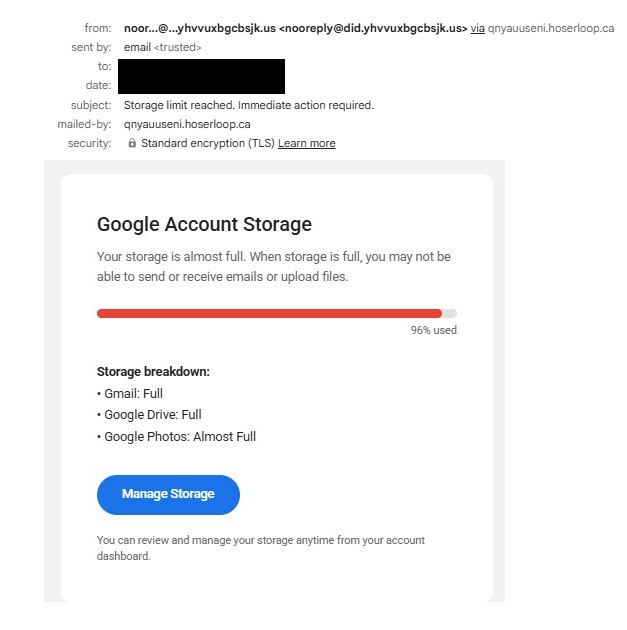
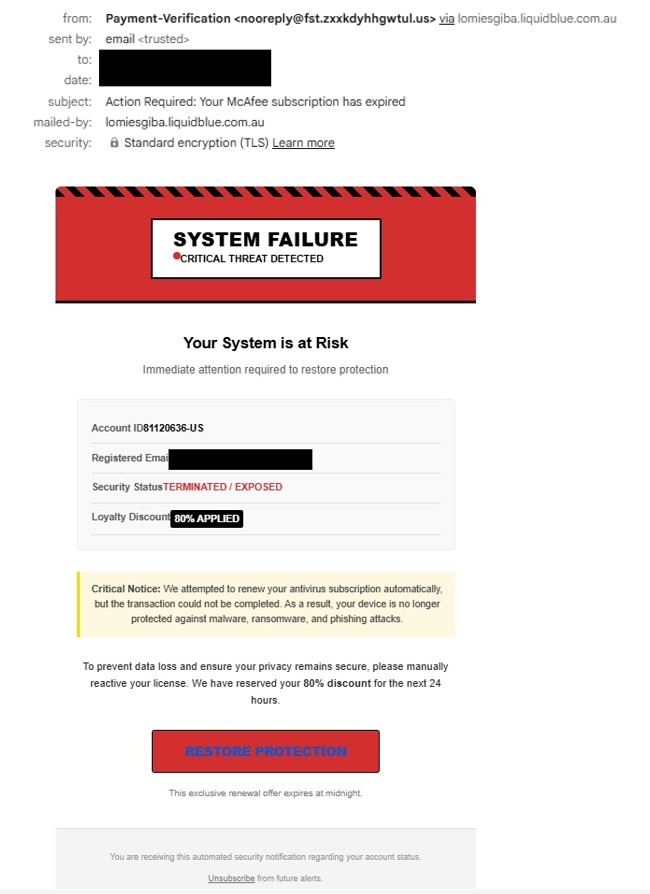
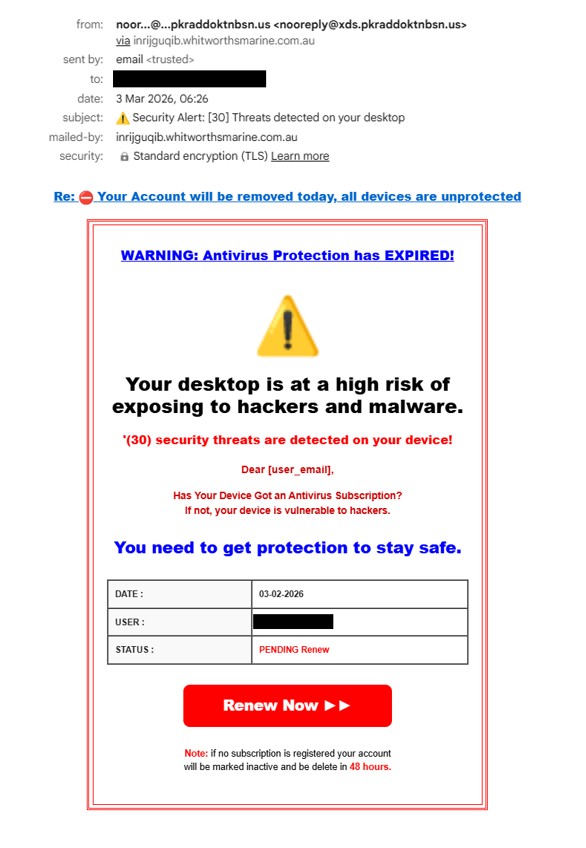
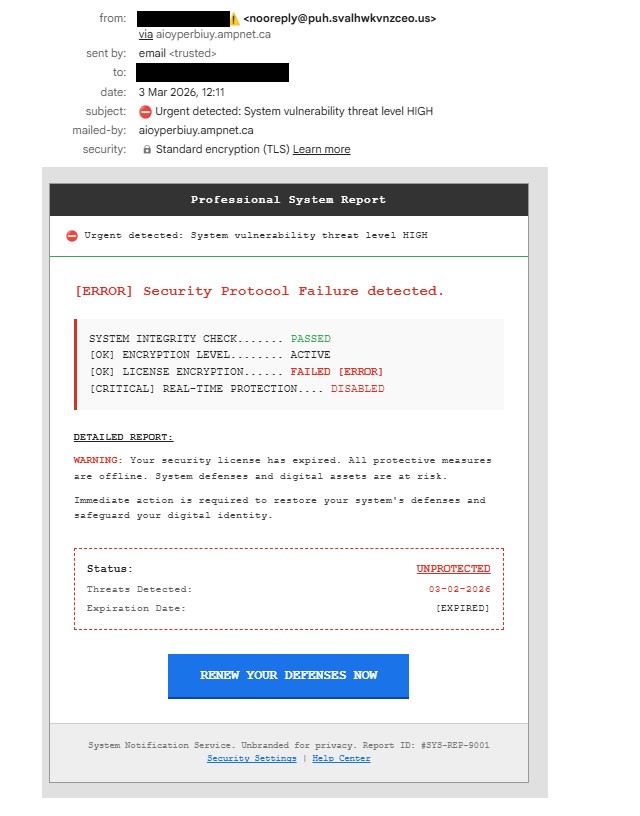
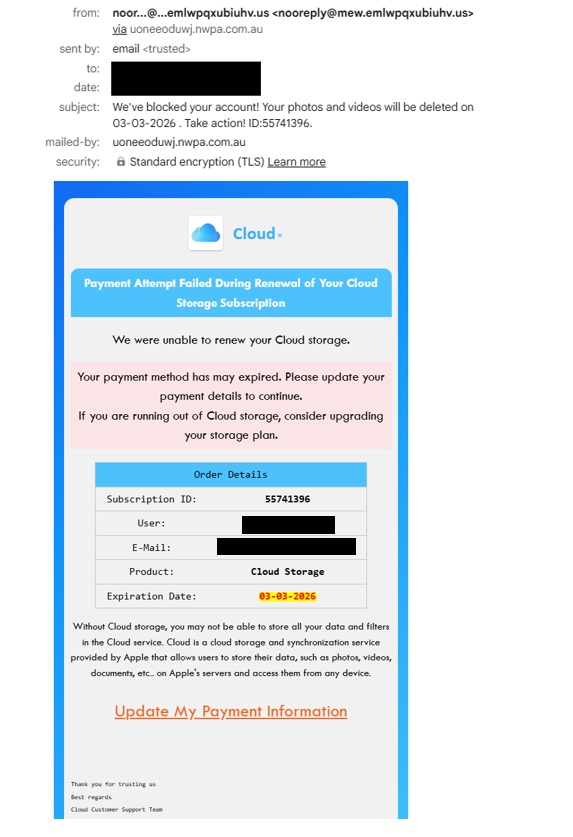
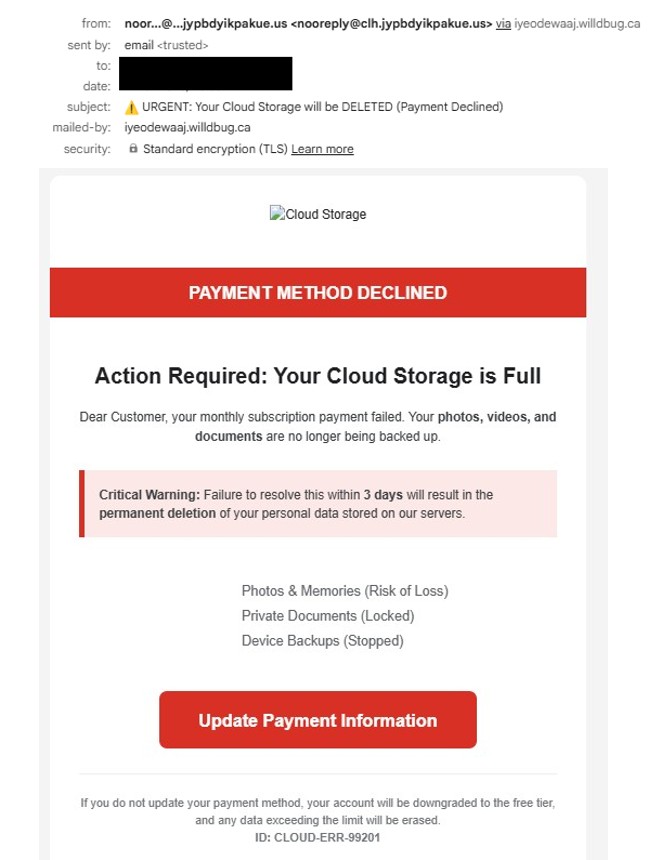
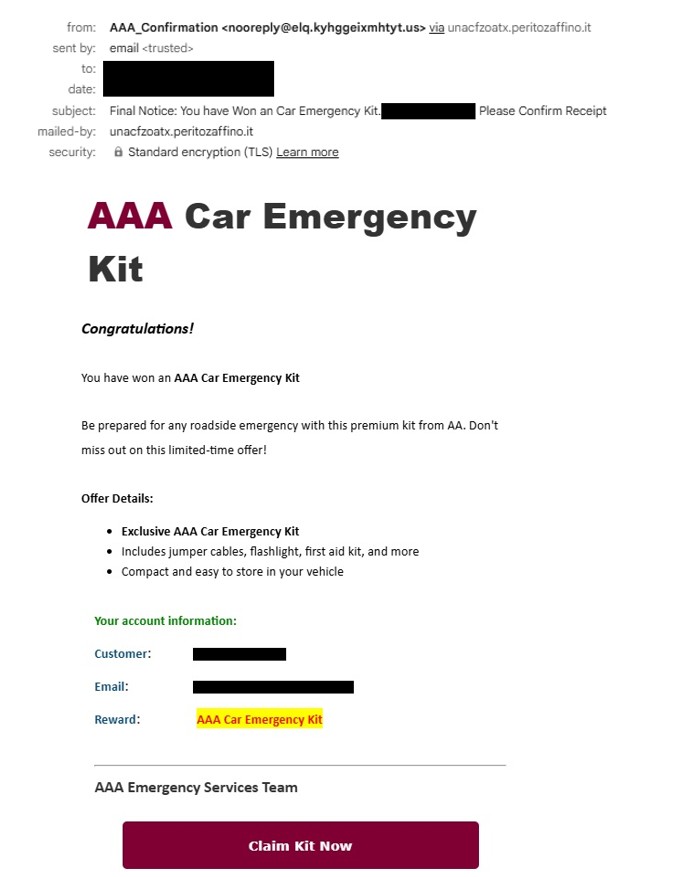
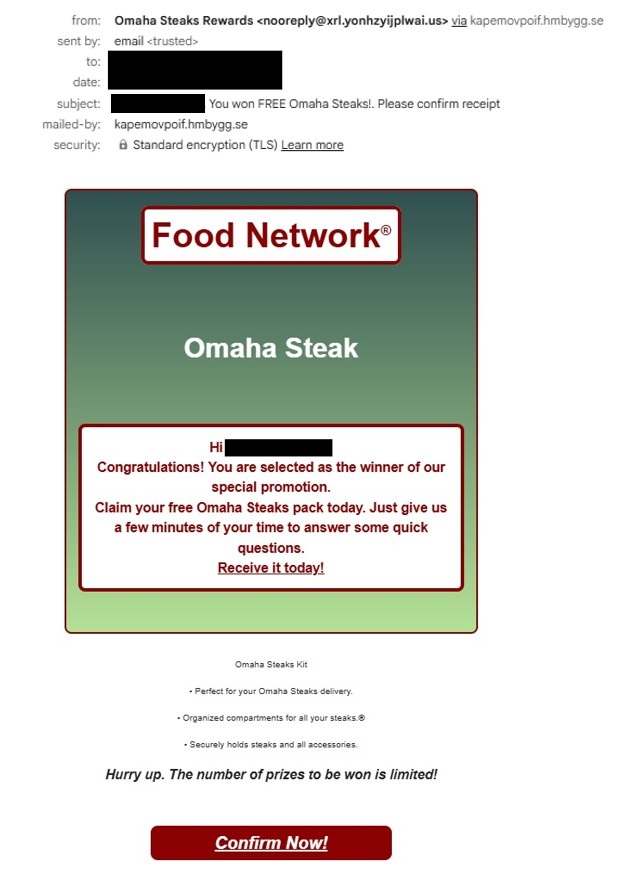
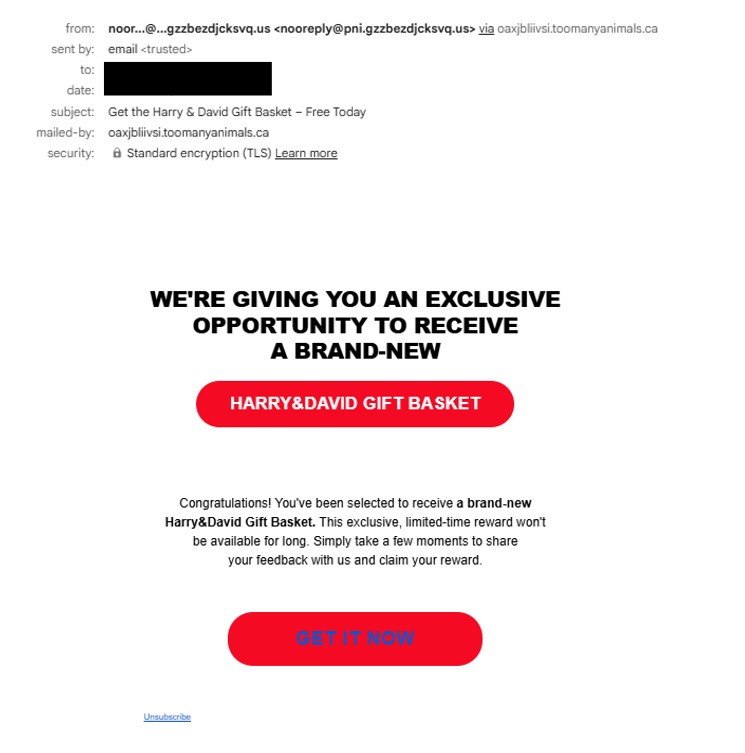
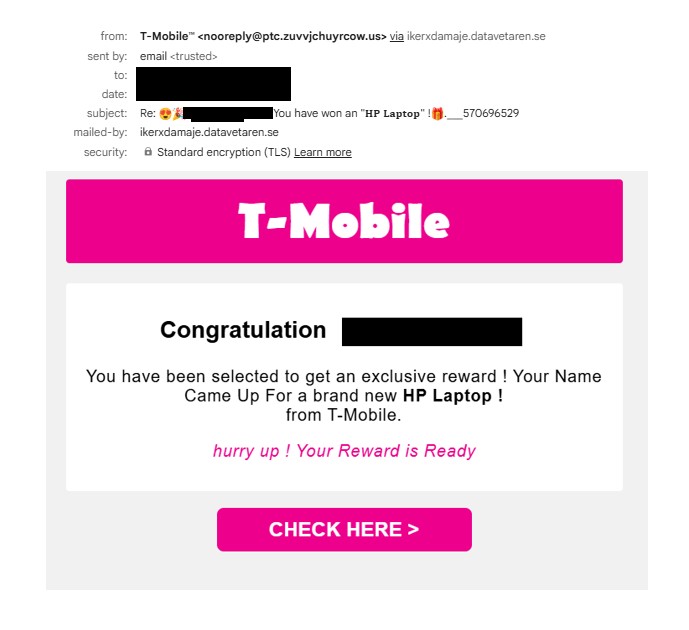
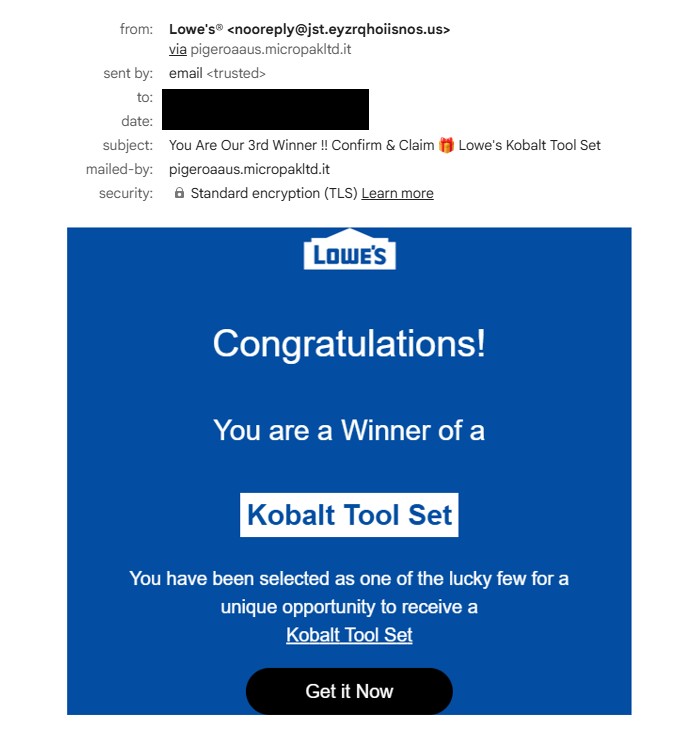
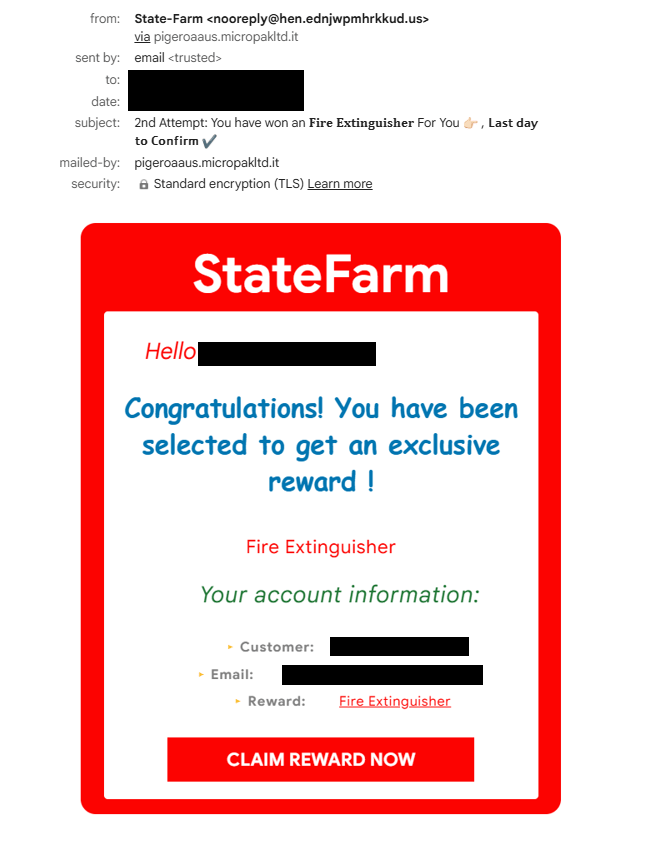
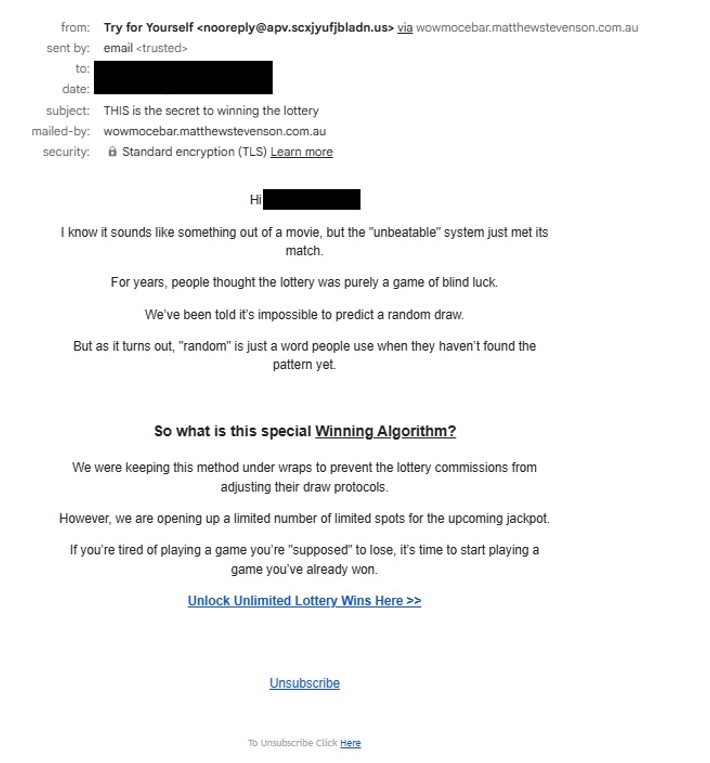
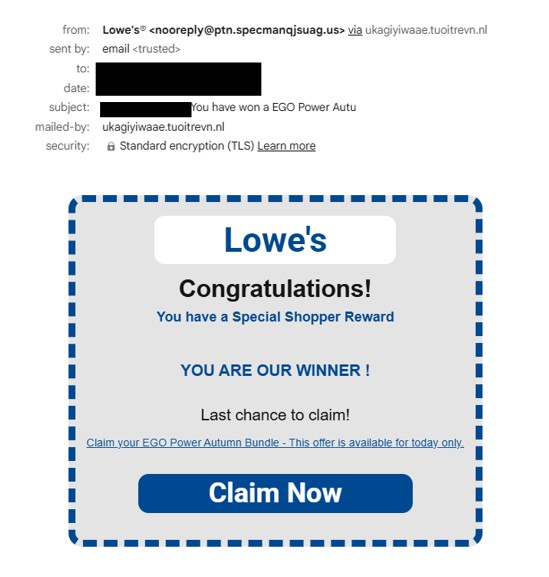
More than 25 emails captured in this study demonstrate an exhaustive range of “hooks” designed to appeal to different psychological triggers. While the underlying technical path is identical, the presentation varies wildly:
- Account Urgency: Notifications claiming “Cloud Storage Full” or “Google Account Storage Full“.
- Security Fears: Alerts regarding a “Critical Threat Detected” or “Antivirus Protection Expired“.
- Retail Incentives: Reward offers from brands such as Lowe’s, T-Mobile, and State Farm.
- Lifestyle & Health: Promotions for “Homemade Recipes“, “Harry & David Gift Baskets“, “Blood Sugar Watch” or “Neuropathy Pain” solutions.
Despite these different themes, the goal remains consistent, drive traffic to the whilewait storage bucket to initiate a fraudulent transaction or steal sensitive information.
The Final Objective: Credit Card Harvesting
Following the redirect from the Google Cloud link, users are typically presented with a “shipping fee” or “service charge” for their reward or security update. This is the Credit Card (CC) Harvesting phase. Any payment information entered on these secondary sites is captured by the attackers, leading to immediate financial fraud. This specific lure mirrors the tactics identified in recent threat research (link given below), where scareware emails are increasingly used to push users toward these fraudulent “subscription” or “service” portals.
Professional Recommendations for Mitigation
To defend against this specific style of “Trusted-Platform Phishing“, the following steps are recommended:
- Inspect the Redirect Path: Be aware that a link starting with storage.googleapis.com is not an official communication from Google, it is a file hosted by a third party using Google’s tools.
- Verify Sender Metadata: Even if the link looks legitimate, the “From” address in these 25 plus samples often consists of unrelated, randomized alphanumeric strings.
- Submit Infrastructure Abuse Reports: These campaigns rely on the longevity of the storage bucket. Reporting the whilewait bucket to the Google Cloud Abuse Team is the most effective way to dismantle the entire 25 plus email network at once.