Phishing emails continue to be a common and sophisticated way for cybercriminals to extort money and sensitive information from unsuspecting individuals. A recent example is an alarming email with the subject line “Your device is hacked,” which tries to create panic, demanding a Bitcoin payment to avoid further consequences.
Subject: Your device is hacked
Good day!
I have to bring something urgent to your notice - you are facing a major challenge. However do not worry just yet; I want you to hear me out, because there's invariably a way to resolution.
Right at this moment, you are subject to the examination of an global web of intruders, and that is a condition that infrequently ends favorably for anyone participating. You may have been informed of groups like Anonymous, nevertheless I guarantee you, we're working on an completely different scale - far beyond what they can offer. Our vast global community comprises countless of proficient experts, each playing a critical role.
Some of our team concentrate on breaching corporate and state systems, while others work stealthily with security agencies on classified missions. My role involves addressing issues tied to clients like you, which is why I am reaching out now.
You might be pondering, "Who are these individuals?" The response is clear: we're concentrated on those with a penchant for alternative and contentious mature content - material that many would deem unsuitable. Nevertheless evidently, you don't fit that type, right?
Allow me to elucidate how I found out this circumstance. A few of weeks ago, we installed stealthy spyware on your device, allowing us access to each your gadgets, including your cellular device. It was straightforward; one of those seemingly harmless pop-ups on private sites served as our entry point.
The good news is you still have a chance to take command of this issue. Let's discuss how you can guard yourself and regain your mental tranquility. Your next moves matter - act intelligently.
We both understand that many people engage in common or even more severe adult content - nothing uniquely unique about that. Nevertheless, the content you've decided to watch transcends a threshold into troubling area.
We've accessed your mobile device and laptop cameras and captured footage of you engaging in acts that are quite debatable. This includes intimate images of you along with the explicit material you were observing.
But remember, there's invariably a path to redemption, including for those who've wandered far. Today, you are blessed because my purpose isn't to inflict pain; I'm simply concentrated on a financial resolution.
This is an opportunity for you to assert control of the situation. Let's talk about how we can resolve this issue cordially.
Here is your rescue: you need to convey $1300 USD in Bitcoin to this digital currency address:
1JxQSshVKAqB9JxuUjmdEDrPN6TM7PzK9D
Let's confront it, that's a fairly insignificant sum in today's society.
I'm reaching out you with an urgent communication that demands your swift attention. You have just 12 hours to complete the payment. Do not delay - act now to safeguard yourself.
As soon as I receive of your transaction, I'll without delay remove all compromising content and fully turn off our computer system. I guarantee you, I honor my promises, even with those who may not fully earn confidence; this is strictly professional.
Nevertheless, if compensation is not received, I will be forced with no choice however to share the damaging videos with everyone in your network - companions, kin, coworkers, associates - everybody. Imagine the unrecoverable damage to your image. This is a blemish that can not ever be fully removed.
The outcomes of doing nothing will not only blemish your identity but could bring you to a point of hopelessness. It is essential to act swiftly.
If you're unfamiliar with digital currency, don't fret - it is easy. A quick search for "cryptocurrency marketplace" will show you how to complete a payment using your credit card. Given your virtual presence, you seem able of handling this with simplicity. Keep in mind, if you've competently traversed the depths of the online world before, this will be no hurdle for you.
Some key reminiscents to reflect on:
- Don't reply to this e-mail. This address is disposable, and any feedback will serve no function.
- Forget about law enforcement. The moment I detect any communication to the police, I will release the data without hesitation.
- Do not attempt to restore or dispose of your gadgets. Such steps are ineffective. My monitoring capabilities mean that I can track your all step.
- It's unfortunate that conditions have brought us here; you could have prevented this situation with more caution online. Be mindful in the future - what seems trivial today can have disastrous consequences tomorrow.
This message is intended as a last notification. Your response in the next 12 hours will determine the consequence of this situation.
Remember, the countdown is running, and the decision is in your control.
Postscript:
If your friends and colleagues were to discover the unethical things you engage in, it could severely harm your relationships and standing. Faith, once damaged, is hard to rebuild, and you might be viewed through a filter of criticism and confusion. This exposure could lead to social isolation, as people may distance themselves from you, being concerned about connection with your behaviors. The taint associated with atypical actions may cause isolation, misinterpretations, or even a damaged image that could hinder your profession possibilities. It is essential to think about the long-term effect this could have on your existence and the connections you value.
In this blog, let’s break down this email and highlight key indicators that mark it as a phishing scam. Recognizing these elements can help you identify similar threats and protect your digital safety.
1. Emotional Manipulation and Psychological Triggers
The first tactic cybercriminals employ is fear. By threatening exposure or embarrassment, they manipulate emotions to push victims into hurried actions. This email opens with an intimidating statement: “you are facing a major challenge.” It follows up with false claims about an elaborate network of hackers monitoring your devices, pushing the recipient into a state of urgency and vulnerability.
2. Specific, Yet General Accusations
The email insinuates that it has incriminating content recorded from the victim’s devices, which could be used for public exposure. However, no specific details or personal information are provided, a common tactic in phishing schemes to keep the accusation vague but ominous. The email accuses the recipient of accessing “controversial mature content” without citing any actual details, casting a wide net to increase its chances of striking fear in potential victims.
3. Unverifiable Technical Claims
Phishing scams often include technical jargon or exaggerated claims to make the message sound more credible. This email alleges that “spyware” was installed through “harmless pop-ups” and implies constant monitoring of all devices. In reality, no malicious software can be this all-encompassing or omniscient. Malware usually requires direct or indirect user permission, such as through a fake download or link, to infiltrate systems.
4. Demand for Payment in Bitcoin
Most phishing emails demand payment in Bitcoin, as cryptocurrency transactions are anonymous and difficult to trace. Here, the email demands $1,300 in Bitcoin within 12 hours, setting a time frame that plays on urgency and limits a recipient’s chances to think critically or consult others.
The specified BTC address has not shown any transactions to date, which thankfully indicates no victims so far.
5. Warnings Against Law Enforcement and No Replies
The sender advises against contacting the police or even responding to the email. By isolating the victim from potential help, the scammer creates a psychological barrier, further increasing the chances of compliance. Additionally, they specify that the email is from a “disposable address,” which reinforces that any reply will be futile.
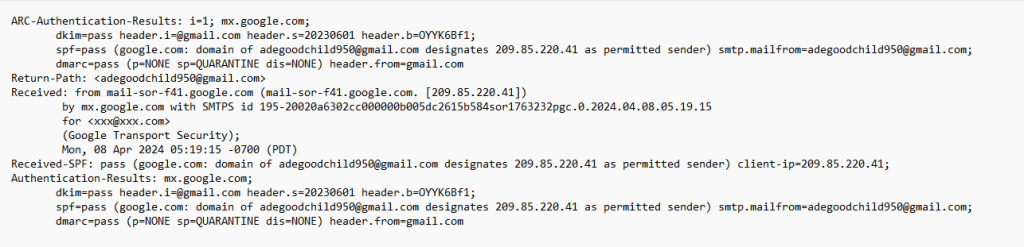
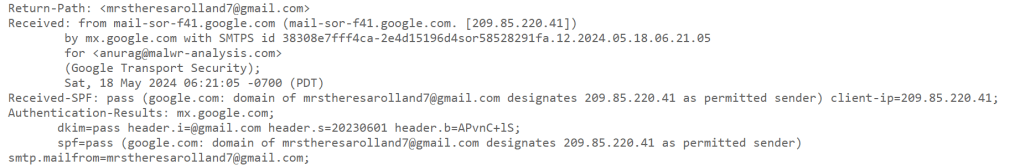
6. Technical Red Flags in the Email Header and Sender Information
A quick analysis of the email header and sender address reveals additional signs of phishing. Although the sender appears as “Lewis Ray info[@]pdparis.com,” the header details a different server (hostglobal.plus) and an untrustworthy IP address with a VirusTotal score of 10/94. This indicates that the IP has previously been associated with malicious activity, solidifying suspicions that this email is not legitimate.
The email header above indicates that the message was received from IP address 78[.]153[.]140[.]175, which has a VirusTotal score of 10/94.
Protective Steps to Take
- Do Not Reply or Pay: Responding or paying emboldens attackers and makes you a potential target for future scams.
- Check Your Security: Ensure that your antivirus and software updates are current. Run scans to ensure no malware or spyware is on your devices.
- Educate and Stay Vigilant: Familiarize yourself with common phishing tactics and educate family or colleagues who may be less aware of cybersecurity risks.
Final Thoughts
Emails like this serve as a reminder of the importance of staying informed about phishing tactics and practicing good cyber hygiene. By recognizing the tactics outlined in this scam email, you can better protect yourself and avoid falling victim to extortion attempts. Remember, if something feels suspicious, it probably is—take a moment to verify, breathe, and never rush to respond to threats like these.